AWS Network Firewall example architectures with routing
This Blog provides a high-level view of simple architectures that you can configure with AWS Network Firewall and shows example route table configurations for each.
Simple single-zone architecture with an internet gateway:
It is a high-level view of a simple VPC configuration using an internet gateway and AWS Network Firewall. It describes the basic route table modifications that are required to use the firewall.
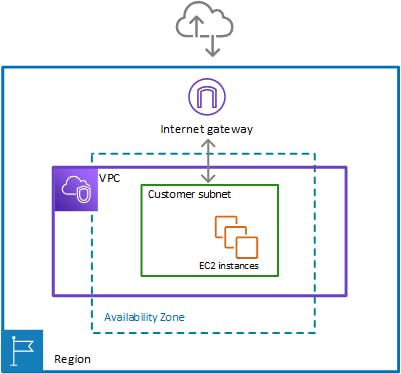
Single zone architecture with internet gateway and no firewall
The following figure depicts a simple VPC configuration with a single customer subnet and no firewall. The VPC has an internet gateway for internet access. All incoming and outgoing traffic routes through the internet gateway to the subnet.
Single zone architecture with internet gateway and the Network Firewall firewall
The following figure depicts a simple VPC configuration with the firewall and the subnet association in place. The VPC has an internet gateway for internet access. All incoming and outgoing traffic for the VPC routes through the firewall.
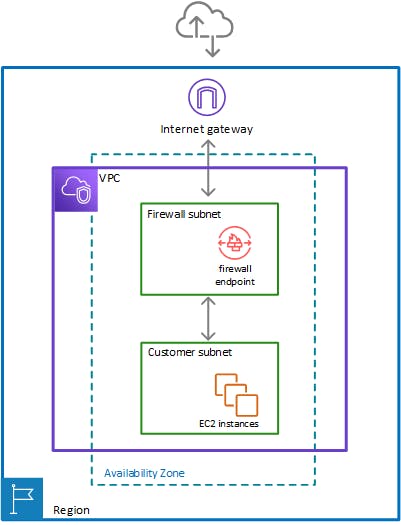
To include the firewall in your Amazon Virtual Private Cloud VPC, you need to modify the VPC route tables so that traffic between the customer subnets and the internet passes through the firewall, for both incoming and outgoing traffic.
Example route tables in the single zone architecture with no firewall
The following figure depicts the route tables that provide the correct flow of traffic for a single Availability Zone without a firewall:
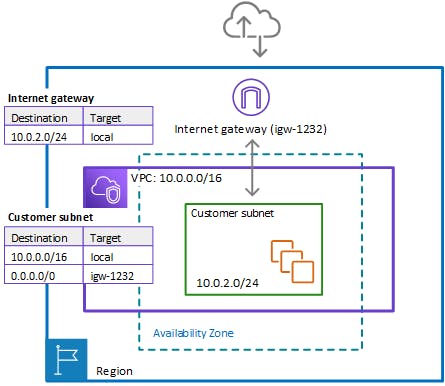
In the preceding figure, the route tables enforce the following traffic flows:
Internet gateway route table – Routes traffic that's destined for the customer subnet (range
10.0.2.0/24) tolocal. The customer subnet shows the private IP address range behind the publicly assigned address. The subnet has public addresses assigned, which are either auto-generated or assigned via Elastic IP address. Within a VPC, only private IP addresses are used for communication.Customer subnet route table – Routes traffic that's destined for anywhere inside the VPC (
10.0.0.0/16) to the local address. Routes traffic that's destined for anywhere else (0.0.0.0/0) to the internet gateway (igw-1232)
Example route tables in the single zone architecture with the firewall
The following figure depicts the same installation with the Network Firewall firewall added and the route tables changed to include the firewall. The route tables direct traffic between the customer subnet and the internet gateway through the firewall endpoint:
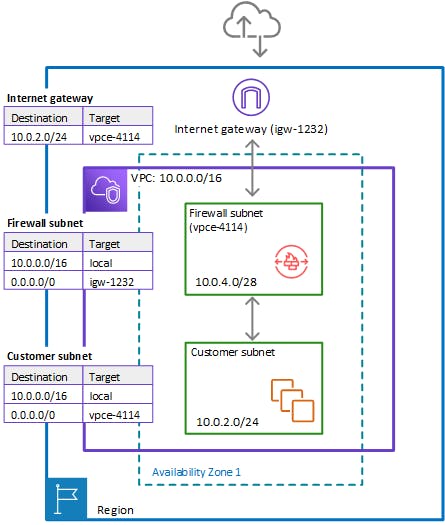
In the preceding figure, the route tables enforce the following traffic flows:
Internet gateway route table – Routes traffic that's destined for the customer subnet (range
10.0.2.0/24) to the firewall subnet (namedvpce-4114in the figure). The customer subnet shows the private IP address range behind the publicly assigned address. The subnet has public addresses assigned, which are either auto-generated or assigned via Elastic IP address. Within a VPC, only private IP addresses are used for communication.Firewall subnet route table – Routes traffic that's destined for anywhere inside the VPC (
10.0.0.0/16) to the local address. Routes traffic that's destined for anywhere else (0.0.0.0/0) to the internet gateway (igw-1232).Customer subnet route table – Routes traffic that's destined for anywhere inside the VPC (
10.0.0.0/16) to the local address. Routes traffic that's destined for anywhere else (0.0.0.0/0) to the firewall subnet (vpce-4114).Before the firewall inclusion, the customer subnet route table routed the
0.0.0.0/0traffic toigw-1232.
Multi-zone architecture with an internet gateway:
high-level view of a simple two-zone VPC configuration using an internet gateway and AWS Network Firewall. It describes the basic route table modifications that are required to use the Network Firewall firewall.
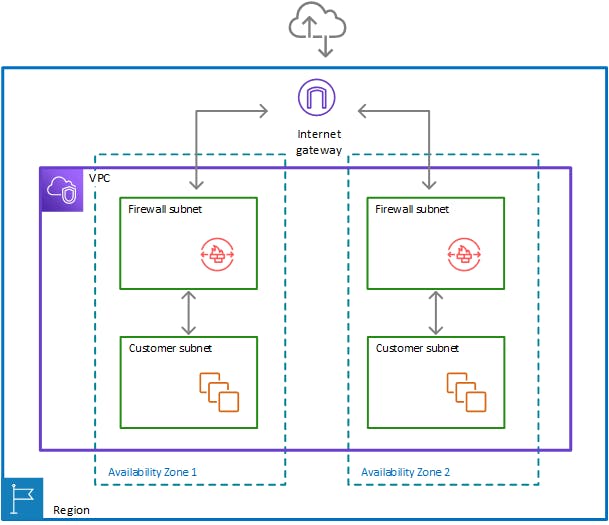
Two-zone architecture with internet gateway and the Network Firewall firewall
The following figure depicts a Network Firewall configuration for a VPC that spans multiple Availability Zones. In this case, each Availability Zone that the VPC spans has a firewall subnet and a customer subnet. The VPC has an internet gateway for internet access. All incoming traffic for the VPC routes to the firewall in the same Availability Zone as the destination customer subnet. All outgoing traffic routes through the firewalls.
Route tables in the two-zone architecture with the firewall
The following figure depicts a VPC configuration with two Availability Zones. Each zone has its own Network Firewall firewall, which provides monitoring and protection for the subnets in the zone. You can expand this configuration to any number of zones in your VPC
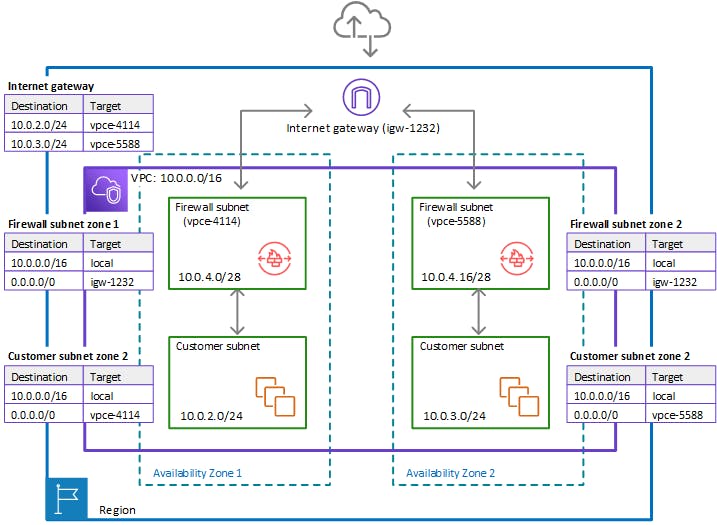
In the preceding figure, the route tables enforce similar traffic flows to the single Availability Zone model, with the primary difference being the splitting of incoming traffic by the internet gateway, to accommodate the two different customer subnets:
Internet gateway route table – Routes traffic that's destined for each customer subnet (range
10.0.2.0/24or10.0.3.0/24) to the firewall subnet in the same Availability Zone (vice-4114orvpce-5588, respectively).Firewall subnet route tables – Route traffic that's destined for anywhere inside the VPC (
10.0.0.0/16) to the local address. Route traffic that's destined for anywhere else (0.0.0.0/0) to the internet gateway (igw-1232). These are identical to the route table for the firewall subnet in the single Availability Zone.Customer subnet route tables – Route traffic that's destined for anywhere inside the VPC (
10.0.0.0/16) to the local address. Route traffic that's destined for anywhere else (0.0.0.0/0) to the firewall subnet in the same Availability Zone (vpce-4114for zone AZ1 andvpce-5588for zone AZ2).
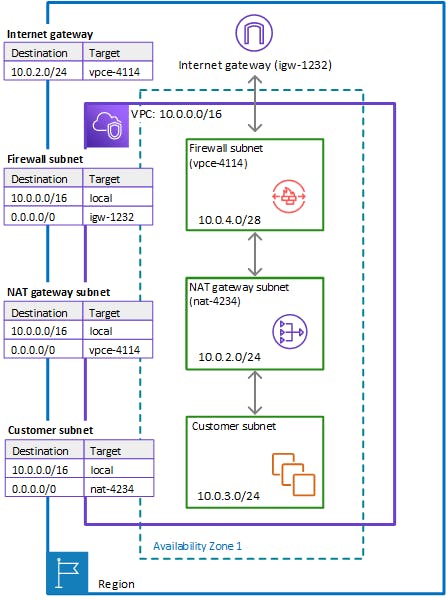
Architecture with an internet gateway and a NAT gateway
You can add a network address translation (NAT) gateway to your AWS Network Firewall architecture, for the areas of your VPC where you need NAT capabilities. AWS provides NAT gateways decoupled from your other cloud services, so you can use it in your architecture only where you need it. This can help you reduce load and load costs. For information about NAT gateways, see NAT gateways in the Amazon Virtual Private Cloud User Guide.
The following figure depicts a VPC configuration for a Network Firewall with an internet gateway and a NAT gateway.
Conclusion:
In wrapping up, we've covered the essentials of implementing AWS Network Firewall with smart routing. By understanding the basics, setting up in a single VPC, extending to multi-VPC scenarios, and ensuring high availability, you've gained insights into crafting a secure network architecture.
STAY TUNED FOR MORE INSIGHTS